 VPNs are great tools that are suitable for everyone, whether it’s those looking for a simple way to unblock a geo-restricted website or those who care about their privacy and want to increase their level of online security. Regardless of the reason, however, some may want to tweak these services for the very best experience. It is well known that for a good streaming session it’s important to prioritize speed over security, but that doesn’t mean the protection level shouldn’t be compromised either. But what happens when security is the number one reason for purchasing a VPN? Surely there are some common notions regarding the choice of protocol and the various different weights of encryption levels, but is nothing more to learn?
VPNs are great tools that are suitable for everyone, whether it’s those looking for a simple way to unblock a geo-restricted website or those who care about their privacy and want to increase their level of online security. Regardless of the reason, however, some may want to tweak these services for the very best experience. It is well known that for a good streaming session it’s important to prioritize speed over security, but that doesn’t mean the protection level shouldn’t be compromised either. But what happens when security is the number one reason for purchasing a VPN? Surely there are some common notions regarding the choice of protocol and the various different weights of encryption levels, but is nothing more to learn?
Knowing Your VPN Service Before Buying
When it comes to commerce we all know how advertising works: every company has the best plans, the best product, and the best prices. In the case of VPNs, the biggest selling points are often fast speeds and full anonymity thanks to the strongest security options. However, only a handful of them actually deliver on this promise, so it’s important to gather as much information as possible about a service and its providing before purchasing.
The first thing security junkies should look for is whether the company respects a no-log policy or not. This is more important than it seems since – when properly respected – it means VPN companies are unaware of the specific actions that its users are taking while connected to the provider’s servers. If not, then you’re just switching one problem for another, as your actions may no longer be visible to your ISP but will still remain fully open to the VPN provider.
The best way to make sure that a company fully respects its no-log policy is to look at the country that it is based in. VPN companies must comply with the law of their country and if this means that they are forced to keep logs or that authorities are permitted to ask for such records – like in the U.S., for instance – then it’s likely that the company does store such data about your use.
Of course, there are exceptions of companies that assure its users that they don’t keep logs even if they must, and these are the ones to pay closer attention to. A good way to tell if a company is secretly holding records is to look for the so-called warrant canaries.
Protocols, Encryptions and Other Features
Even if a company does seem to firmly stick to its no-log policy, the product itself can raise some doubts. This is where reading our detailed reviews will help out, since it’s hard for most users to test the service themselves without suffering from certain negative effects that can sometimes have damaging outcomes.
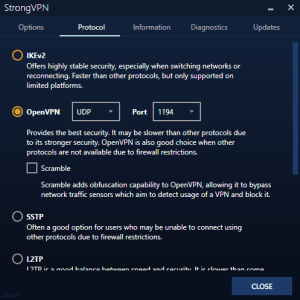
Most VPNs nowadays use the standard 256-bit security encryption, a military-grade level of encryption that is unbreakable to date and protects traffic against the prying eyes of intruders and ISPs. This is another major selling point advertised by these companies and is a very important aspect to look for, but often it’s not something that users have access to. On the other hand, a good VPN service will give users some settings to allow them to alter between a lighter or heavier encryption. This is often done indirectly, though, by allowing them to switch protocols or ports. It’s true that some knowledge is required to know which protocol is the best for any occasion, but in most cases this is enough to fine tune the VPN for better security.
 On top of that, it’s also a good idea – particularly for torrenters – to enable the kill switch function whenever that’s an option, since this will stop all internet connections if the VPN disconnects suddenly.
On top of that, it’s also a good idea – particularly for torrenters – to enable the kill switch function whenever that’s an option, since this will stop all internet connections if the VPN disconnects suddenly.
But even more important than all this is a feature to check for DNS leaks, which is a silent menace that is often ignored by many users. Many VPNs send users to the settings to choose to activate this protection or not, though most of them state that this function is enabled by default. The latter are the ones you need to be more careful about since a DNS leak essentially reveals your real physical location as traffic is not – however temporarily – successfully routed through an anonymous network. In turn, this means that not only are ISPs able to see your online activity even when using the VPN, but hackers and other intruders can also redirect you to all kinds of fraudulent websites.
Best VPN Services of 2024
| Rank | Provider | Info | Visit |
1
|
Editor's Choice 2024

|
|
|
2
|
|
||
|
3
|

|
|
Get the Best VPN Deals
Want to stay up to date on the latest VPN news and discounts? Get exclusive offers and deals sent straight to your inbox!
Share Your Comment